Good day
I have a customer running on 20 ALE switches with a mixture between 2260 and 2360 running UNP’s for Data VLAN 10, Voice VLAN 869 and WLAN AP’s VLAN 100 with multiple VLAN’s for the WLAN SSID’s. I have a problem where there are Ubiquiti Unifi AP’s connected and placed into VLAN 100 via a UNP OUI which is working, but the problem is that there are often users connecting to the WLAN and gets “Blocked” by the switch and some users connect with no issue. Is there anyone who has experienced this or might know what the cause is? I will paste my UNP config below as well as an output with command “show unp user” where the switch is blocking users.
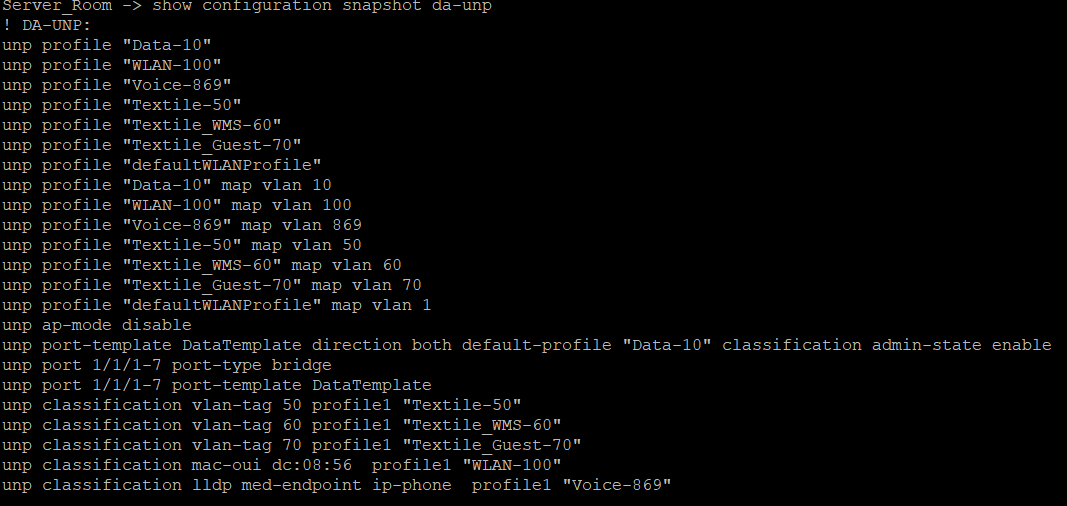
! DA-UNP:
unp profile “Data-10”
unp profile “Voice-869”
unp profile “Maytex_WLAN”
unp profile “defaultWLANProfile”
unp profile “Data-10” map vlan 10
unp profile “Voice-869” map vlan 869
unp profile “Maytex_WLAN” map vlan 100
unp profile “defaultWLANProfile” map vlan 1
unp port-template DataTemplate direction both default-profile “Data-10” classification ap-mode admin-state enable
unp port 1/1/1-44 port-type bridge
unp port 1/1/1-44 port-template DataTemplate
unp classification mac-oui 60:22:32 profile1 “Maytex_WLAN”
unp classification lldp med-endpoint ip-phone profile1 “Voice-869”
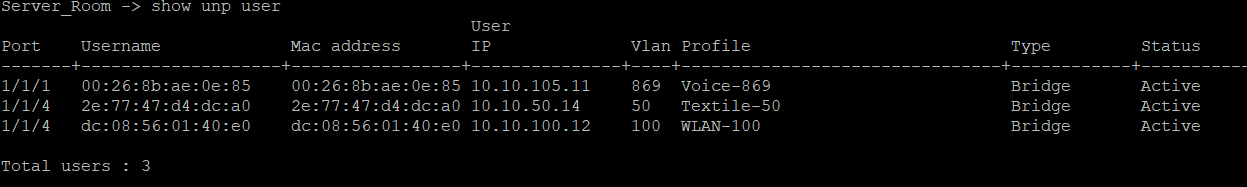
Port Username Mac address IP Vlan Profile Type Status
-------±-------------------±----------------±--------------±—±-------------------------------±-----------±----------
1/1/1 24:9a:d8:a6:63:bc 24:9a:d8:a6:63:bc 192.168.105.50 869 Voice-869 Bridge Active
1/1/2 60:22:32:7e:a2:81 60:22:32:7e:a2:81 - 70 - Bridge Block
1/1/2 60:22:32:7e:a2:81 60:22:32:7e:a2:81 10.0.100.4 100 Maytex_WLAN Bridge Active
1/1/2 d4:0a:dc:51:6d:99 d4:0a:dc:51:6d:99 - 70 - Bridge Block
1/1/3 2c:0e:3d:9d:4d:bb 2c:0e:3d:9d:4d:bb - 81 - Bridge Active
1/1/3 60:22:32:6e:93:3c 60:22:32:6e:93:3c 10.0.100.5 100 Maytex_WLAN Bridge Active
1/1/3 d2:51:9a:01:87:45 d2:51:9a:01:87:45 10.0.12.50 50 - Bridge Active
1/1/3 dc:21:5c:06:51:df dc:21:5c:06:51:df 10.0.12.92 50 - Bridge Active
1/1/3 f2:29:f2:80:da:84 f2:29:f2:80:da:84 10.0.12.81 50 - Bridge Active
1/1/4 38:fc:98:10:9e:c9 38:fc:98:10:9e:c9 10.0.12.102 50 - Bridge Active
1/1/4 60:22:32:7e:86:55 60:22:32:7e:86:55 10.0.100.3 100 Maytex_WLAN Bridge Active
1/1/4 8a:35:5e:14:1a:03 8a:35:5e:14:1a:03 10.0.13.68 70 - Bridge Active
1/1/4 92:b0:8d:ba:f6:32 92:b0:8d:ba:f6:32 10.0.12.82 50 - Bridge Active
1/1/5 60:22:32:85:7d:c5 60:22:32:85:7d:c5 10.0.100.2 100 Maytex_WLAN Bridge Active
1/1/7 6c:0b:5e:56:ab:30 6c:0b:5e:56:ab:30 10.0.8.254 10 Data-10 Bridge Active
1/1/13 44:8a:5b:b5:bc:29 44:8a:5b:b5:bc:29 10.0.8.211 10 Data-10 Bridge Active
1/1/15 44:db:d2:42:5d:10 44:db:d2:42:5d:10 192.168.105.58 869 Voice-869 Bridge Active
1/1/15 64:00:6a:46:46:5b 64:00:6a:46:46:5b 10.0.8.238 10 Data-10 Bridge Active
1/1/16 24:9a:d8:95:fc:a1 24:9a:d8:95:fc:a1 192.168.105.61 869 Voice-869 Bridge Active
1/1/16 e0:70:ea:d9:f4:27 e0:70:ea:d9:f4:27 10.0.8.236 10 Data-10 Bridge Active
1/1/17 24:9a:d8:91:db:aa 24:9a:d8:91:db:aa 192.168.105.54 869 Voice-869 Bridge Active
1/1/17 d8:9e:f3:9b:7d:fb d8:9e:f3:9b:7d:fb 10.0.8.218 10 Data-10 Bridge Active
1/1/18 24:9a:d8:86:3d:fe 24:9a:d8:86:3d:fe 192.168.105.60 869 Voice-869 Bridge Active
1/1/18 c0:25:a5:9b:48:e1 c0:25:a5:9b:48:e1 10.0.8.248 10 Data-10 Bridge Active
1/1/23 00:17:c8:9f:4d:bb 00:17:c8:9f:4d:bb 10.0.8.20 10 Data-10 Bridge Active
1/1/24 00:24:9b:4f:4a:20 00:24:9b:4f:4a:20 10.0.8.253 10 Data-10 Bridge Active
1/1/43 04:03:12:19:8d:5b 04:03:12:19:8d:5b 10.0.8.242 10 Data-10 Bridge Active
1/1/44 e0:2e:fe:56:ee:53 e0:2e:fe:56:ee:53 10.0.8.209 10 Data-10 Bridge Active
Total users : 28